- sales@smartpro.vn | tuvan@smartpro.vn
- (028) 39 333 376 | 0943 338 846
- Vietnamese | English
Secure Windows Servers with Role-Based User Access
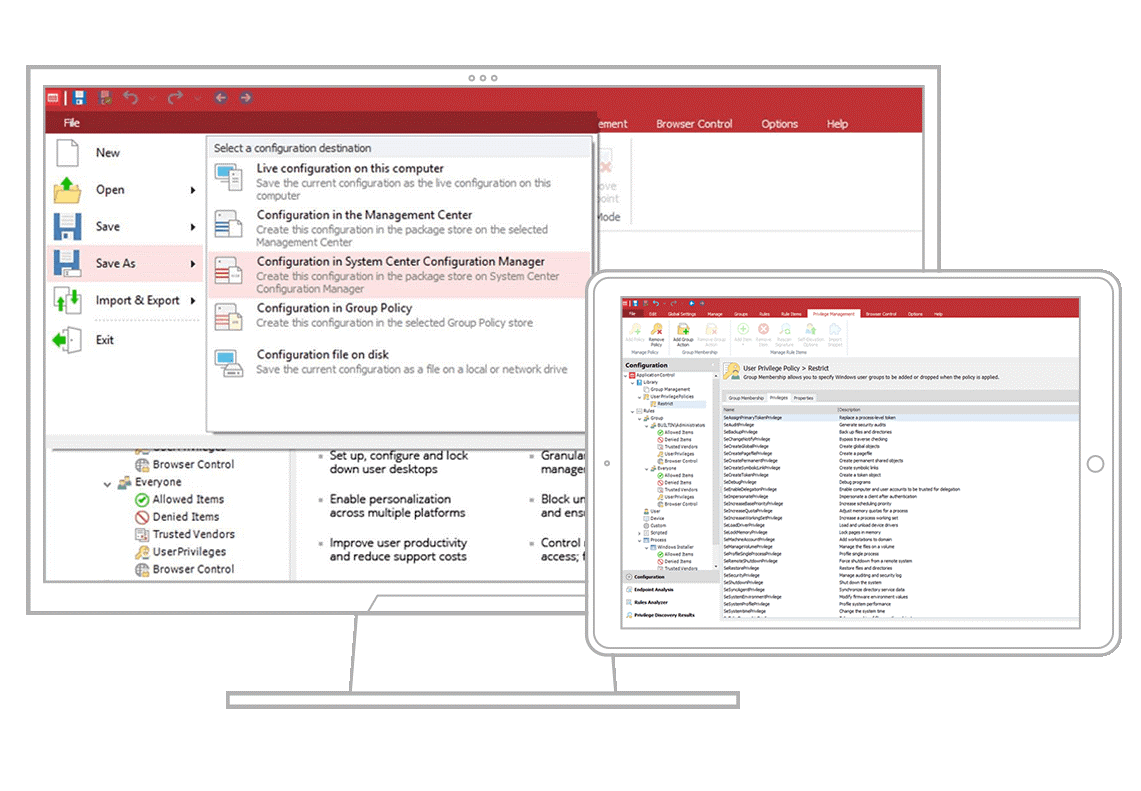
Ivanti® Application Control for Windows Server lets you control server access and reduce risk by limiting the administrative rights of users who must log onto a server to perform specific, job-related tasks. This is especially advantageous if the server is multi-purpose (for example, SQL and IIS) with multiple admin users, or if the organization must comply with regulations that dictate computing infrastructure security practice.
Limit users to performing specific tasks only when logging onto servers
Using Ivanti Application Control for Windows Servers, IT can limit administrative privilege to specific consoles, applications, services, and commands, reducing the risk of admins introducing malware, halting essential services, or affecting performance of mission-critical services.
Privilege Elevation
Providing full admin rights on a server to users untrained as IT system administrators creates multiple risks, like starting or stopping services and installing or removing software in error. This can increase security risk and manageability costs, decrease productivity, create legal and liability issues, and make it difficult to achieve compliance. By removing full admin rights from users and providing them with elevated privileges for just the tasks they need for their job, you can
simplify endpoint security, reduce support calls, and lower TCO.
Application Control
Ivanti Application Control for Windows Servers allows authorized access to server applications, services, and components, based on application whitelisting. Using Application Control, IT can assign an SHA-1, SHA-256, or ADLER32 digital signature to ensure file integrity. Additionally, IT can check file metadata – including vendor, certificate, publisher, version, and more – to ensure applications, components, and scripts are original and are preventing modified or spoofed applications from executing.
System Controls Protection
Apply System Controls to elevate or restrict access to specific services, prevent removal or modification of server applications and processes, and prevent clearing of named event logs.